TL;DR: Data protection clauses are no longer boilerplate - they're a core contract negotiation item. In 2025-26, every SaaS, cloud, or AI vendor deal requires a solid DPA that addresses: (1) controller-processor roles, (2) permitted uses (especially AI training), (3) sub-processor controls, (4) cross-border transfer mechanisms, (5) breach notification timelines, (6) data subject rights, and (7) deletion timelines. Get it wrong, and you face regulatory fines measured in millions, plus indemnity claims from your vendor if they prove the breach was your fault. Spend time on the DPA schedule - it's the appendix that actually matters.
What is a Data Protection Clause?
Data protection clauses sit at the intersection of contract law and regulatory compliance. They're not optional - GDPR, CCPA, COPPA, and dozens of other regimes require them. The clause defines the relationship between a data controller (you, the company) and a data processor (a vendor handling your customer data). Without a proper data protection agreement in place, both parties can face fines measured in millions.
The regulatory environment exploded in 2025-26. The EU AI Act became enforceable across Europe, adding new data classification requirements for AI training data. The US state privacy law patchwork - CPRA in California, VCDPA in Virginia, CPA in Colorado, CTDPA in Connecticut - created a compliance minefield. India's DPDP Act (2023) and China's PIPL added data localization and sovereignty requirements that force vendors to physically store data on local infrastructure. The Schrems II ruling still haunts EU-US data transfers, and while the EU-US Data Privacy Framework finally provided a mechanism for transatlantic data flow, it remains politically fragile. Meanwhile, Meta has faced GDPR enforcement actions exceeding 2 billion euros, making privacy a board-level liability issue.
A solid data protection clause clarifies: what personal data is being processed, where it's stored and processed, who can access it, how it's deleted, and what happens if it's breached. It also establishes who owns the liability if things go wrong - typically, the data controller (you) bears the responsibility to regulators, but the processor (your vendor) indemnifies you if the breach was their fault.
Critical data protection elements:
• Data processing obligations - what the processor can and cannot do with personal data
• Sub-processor controls - who else can touch the data (cloud providers, analytics vendors, etc.)
• Cross-border transfer mechanisms - Standard Contractual Clauses (SCCs) or other approved mechanisms for moving data between jurisdictions
• Breach notification - timeline and process for reporting security incidents
• Data subject rights - how to handle requests to access, delete, or port personal data
• Data retention and deletion - when data gets purged and how
• DPA (Data Processing Agreement) as a separate, binding schedule
Data Controller vs. Data Processor Responsibilities
- Controller is the organization that determines the purposes and means of processing personal data. If you're a SaaS company collecting customer usage data, you're the controller. You decide what data to collect, how long to keep it, and what you use it for. Controllers bear the primary regulatory burden - compliance with GDPR, CCPA, COPPA, etc. falls on you.
- Processor is the vendor who processes data on the controller's behalf. They handle it in the way the controller instructs. A cloud hosting provider or a payment processor is typically a processor. Processors have limited liability for regulatory violations (they can't be fined under GDPR for not obtaining consent, for instance) but they're responsible for implementing technical and organizational security measures.
- Joint controllers can exist when two organizations together decide how and why data is processed - think of a co-marketing arrangement where both parties decide to collect leads jointly. Joint controllers share liability and must coordinate with each other.
- AI training data is personal data: In 2025-26, regulators clarified that using personal data to train AI models is "processing," and it requires a lawful basis. If you're training a model on customer data without explicit consent, you've violated GDPR. This has become a critical issue for vendors delivering AI services.
Cross-Border Transfers and Data Localization
- Standard Contractual Clauses (SCCs) were the primary tool for moving personal data between GDPR-regulated entities and processors in non-adequate countries (US, India, etc.). Post-Schrems II, SCCs are still legal but they require an assessment of the country's surveillance laws. If the US NSA or GCHQ can easily access EU data, SCCs may not hold up in court.
- EU-US Data Privacy Framework (2023) provides a streamlined mechanism for adequacy decisions on specific US companies certified as "adequate." Microsoft, AWS, and others obtained certification. However, the framework remains politically fragile and could be revoked if US surveillance practices become more aggressive.
- Data sovereignty and localization: India's DPDP Act and China's PIPL require sensitive data to stay within their borders. This means vendors must either maintain local infrastructure or avoid processing that data entirely. For global vendors, it means separate data flows for India/China vs. rest-of-world.
- Children's data and COPPA 2.0: US COPPA (Children's Online Privacy Protection Act) protections expanded in 2025, extending privacy obligations to kids under 13. Any service targeting children needs explicit parental consent, limited data collection, and strict retention policies. Similarly, UK ICO strengthened COPPA-like protections for children.
A well-drafted Data Protection Clause contains:
- Scope and definitions: "Personal data" means any information relating to an identified or identifiable natural person. Define what categories of personal data you're processing (emails, transaction history, location, biometric, health data, etc.) because different categories may have different regulatory treatments.
- Processing instructions: The processor will only process personal data on documented written instructions from the controller, and only for the purpose specified in the DPA. This pins down the processor's obligations - they can't repurpose the data.
- Sub-processor authorization: The processor identifies all sub-processors (AWS, Stripe, Segment, etc.) upfront and commits to binding SCCs or equivalent terms with each sub-processor. The controller can object to new sub-processors. This prevents surprise outsourcing to unknown vendors.
- Technical and organizational security measures: The processor implements appropriate security - encryption, access controls, monitoring, incident response procedures. This aligns with GDPR Article 32 requirements.
- Breach notification: If the processor discovers a breach, they notify the controller without undue delay (within 72 hours is standard) so the controller can meet its regulatory reporting deadlines.
- Data subject rights: If a customer asks to see their data or delete it, the processor cooperates with the controller's response. The controller is responsible for fulfilling the request, but the processor must provide the underlying data or tools to do it.
- Audit and compliance: The processor documents its compliance with GDPR/CCPA/local law and allows the controller to audit (or hire an auditor to audit) the processor's security practices. Many enterprise deals include SOC 2 Type II attestations.
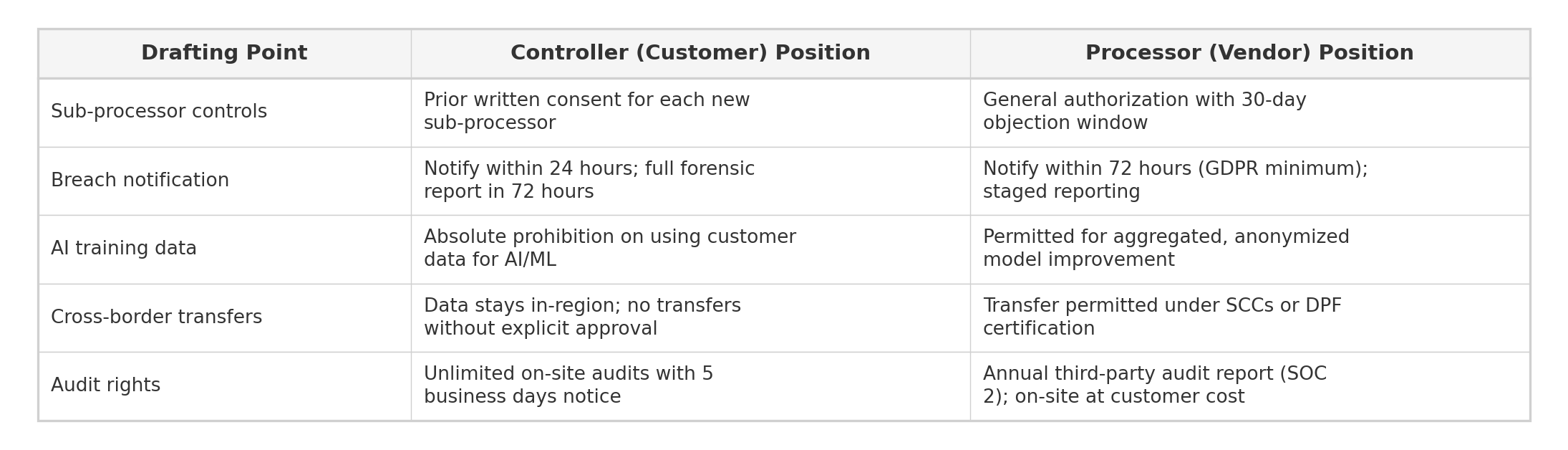
Market Position & Benchmarks
Where Does Your Clause Fall?
- Controller-Favorable: Strict processing limitations with no permitted secondary use, prior written consent required for every sub-processor, 24-hour breach notification, unlimited audit rights (on-site, with minimal notice), controller retains all IP in processed data, processor bears full indemnity for any breach of the DPA, and data localization requirements restricting processing to specific jurisdictions.
- Balanced/Market Standard: Processing limited to documented instructions with a narrow "legitimate business operations" carve-out, general authorization for sub-processors with 30-day advance notice and objection rights, 48-72 hour breach notification, annual audit rights (or acceptance of SOC 2 Type II reports as a substitute), shared liability based on respective fault, and SCCs or Data Privacy Framework certification for cross-border transfers.
- Processor-Favorable: Broad processing permissions including aggregated and anonymized data for service improvement, general sub-processor authorization with notification only (no objection right), 72-hour breach notification measured from confirmation rather than discovery, audit limited to third-party certification reports, capped liability tied to fees paid, and processor retains rights to de-identified data for benchmarking and product development.
Market Data
- Over 92% of enterprise SaaS contracts now include a standalone Data Processing Agreement (DPA) as a required schedule, up from approximately 60% in 2020 (IAPP Vendor Management Survey, 2025).
- Breach notification timelines in negotiated DPAs average 48 hours from discovery; approximately 35% of enterprise buyers successfully negotiate 24-hour notification, while the GDPR statutory default is 72 hours (without undue delay).
- Sub-processor objection rights with a contractual right to terminate appear in roughly 70% of enterprise DPAs. The remaining 30% provide notification only, with no meaningful objection mechanism.
- Cross-border transfer mechanisms in surveyed contracts break down as follows: SCCs alone (45%), EU-US Data Privacy Framework plus SCCs as fallback (30%), Binding Corporate Rules (10%), and data localization commitments (15%).
- GDPR enforcement fines exceeded 4.4 billion euros cumulatively through 2025, with the largest single fine reaching 1.2 billion euros (Meta, 2023). The average fine for DPA violations specifically (inadequate processor agreements) is approximately 350,000 euros.
- AI training data restrictions now appear in 65% of newly negotiated enterprise DPAs, prohibiting the processor from using controller data to train machine learning models without explicit written consent (Gartner Legal Technology Survey, 2025).
Sample Language by Position
Controller-Favorable: "Processor shall process Personal Data solely in accordance with Controller's documented written instructions and exclusively for the purpose of providing the Services. Processor shall not process, transfer, modify, or otherwise use Personal Data for any other purpose, including aggregation, anonymization, benchmarking, analytics, or model training. Processor shall notify Controller of any Personal Data Breach within twenty-four (24) hours of becoming aware of such breach. Controller shall have the right to conduct on-site audits of Processor's data processing operations upon thirty (30) days' written notice, at Controller's expense. Processor shall not engage any sub-processor without Controller's prior specific written consent for each sub-processor."
Balanced/Market Standard: "Processor shall process Personal Data only on Controller's documented instructions and for the purposes specified in the DPA. Processor may use aggregated, de-identified data for internal service improvement, provided that re-identification is not practically feasible. Processor shall notify Controller of any Personal Data Breach without undue delay, and in any event within seventy-two (72) hours of becoming aware of such breach. Controller may audit Processor's compliance annually, or may accept Processor's current SOC 2 Type II report and penetration test results as a reasonable substitute. Processor shall provide Controller with at least thirty (30) days' advance notice before engaging a new sub-processor; Controller may object in writing within that period."
Processor-Favorable: "Processor shall process Personal Data in accordance with Controller's instructions as set forth in the Agreement. Processor may process de-identified and aggregated data derived from Personal Data for service optimization, benchmarking, and product development purposes. Processor shall notify Controller of any confirmed Personal Data Breach within seventy-two (72) hours of confirming such breach. Controller may review Processor's most recent SOC 2 Type II report and security certifications upon request; on-site audits shall be limited to once per year with sixty (60) days' advance notice. Processor shall maintain a current list of sub-processors and notify Controller of any changes."
Example language:
Data protection clauses typically include dense legalese, but here's the skeleton:
- Short version: "Vendor shall process personal data only on Controller's documented instructions. Vendor shall not disclose personal data to third parties except to approved sub-processors under equivalent terms. Vendor shall implement technical and organizational security measures appropriate to the risk level, including encryption of data in transit and at rest. Vendor shall notify Controller of any suspected breach within 24 hours."
- Full compliance version: Includes a detailed DPA schedule specifying data categories, transfer mechanisms (SCCs, BCRs, etc.), sub-processor list, security audit procedures, deletion timelines, GDPR Article 32 obligations, and liability allocation.
Sample Clause Language:
Example 1: GDPR/CCPA Compliant Data Processing Agreement
"Processor shall process personal data only on documented written instructions from Controller. Processor shall: (a) ensure that persons authorized to process personal data have committed to confidentiality; (b) implement and maintain appropriate technical and organizational measures to protect personal data, including encryption in transit and at rest, access controls, and logging; (c) not disclose personal data to any sub-processor without prior written authorization from Controller, and shall ensure all sub-processors are bound by equivalent data protection terms; (d) assist Controller in meeting its obligations to data subjects (access requests, deletion requests, portability); (e) at Controller's request or on Controller's behalf, delete or return all personal data after the end of the service provision, unless EU law or applicable law requires storage; (f) notify Controller without undue delay upon becoming aware of a personal data breach, and shall cooperate fully in any investigation or regulatory notification; (g) make available to Controller all information necessary to demonstrate compliance with GDPR Article 28-32 and allow for audits or inspections."
Example 2: AI Training Data Carve-Out and Consent Mechanism
"Notwithstanding the foregoing, Processor shall NOT use personal data for any purpose other than providing the Services, except where (i) Controller provides explicit written consent for specific AI model training, (ii) the processing is anonymized such that data subjects cannot be re-identified, or (iii) the processing is required by law. Processor shall maintain a separate consent log documenting Controller's authorization for any AI training use. If Processor intends to use aggregated or anonymized data for model improvement, Processor shall provide Controller with a detailed technical description of the anonymization methodology and retain an independent auditor to certify that re-identification is not practically feasible."
Contract types where Data Protection Clause is critical:
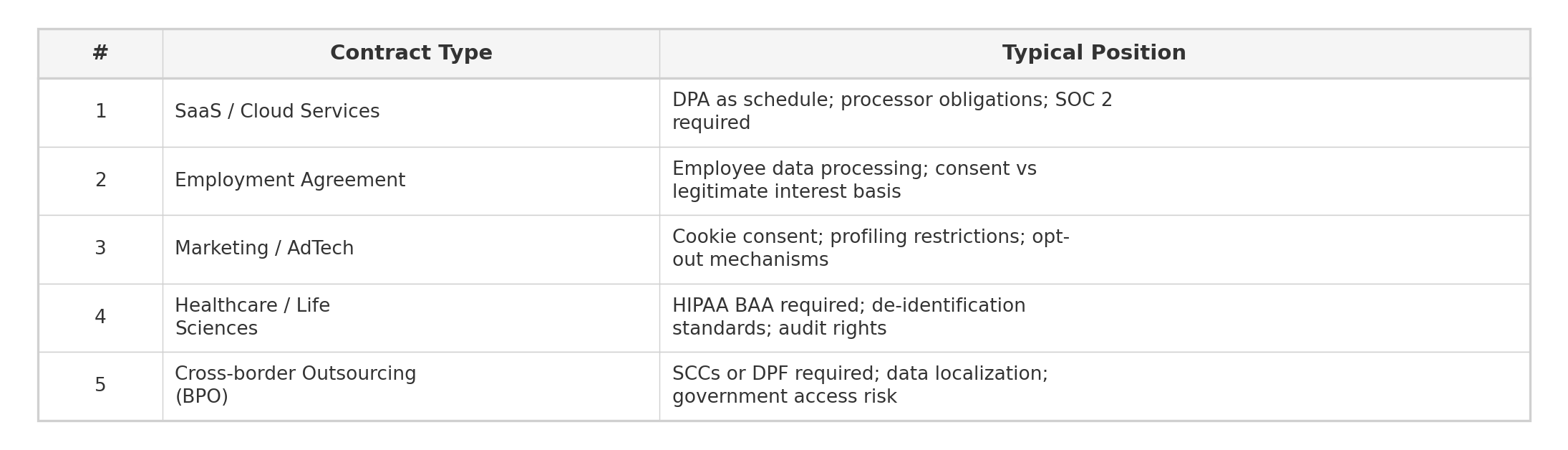
Common structures and market practices:

Negotiation Playbook
Key Drafting Notes
- Get controller-processor classification right from the start: Misclassifying the relationship is the most common and most consequential DPA error. If your vendor uses your customer data for its own analytics, product improvement, or AI training, it is a controller or joint controller for those purposes, not a processor. The classification determines liability allocation, regulatory obligations, and audit rights. Review the vendor's actual data practices, not just what they call themselves.
- Negotiate breach notification timelines aggressively: The GDPR requires controller notification to regulators within 72 hours, which means you need to know about a breach well before that deadline. Push for 24-hour notification from discovery (not from "confirmation"). Include specific information the processor must provide in the initial notice: nature of the breach, categories and approximate number of data subjects affected, likely consequences, and measures taken or proposed.
- Require a living sub-processor list with meaningful objection rights: A static sub-processor list at signing is insufficient. Require the processor to maintain a current list (typically on a public URL) and provide at least 30 days' advance notice before adding a new sub-processor. Secure a contractual right to object, with termination for convenience as the backstop if the processor proceeds over your objection. Without this termination right, the objection mechanism has no teeth.
- Address AI and machine learning use explicitly: Standard DPA language written before 2023 does not address AI model training. Add an explicit prohibition on using personal data (including metadata, usage patterns, and interaction logs) to train, fine-tune, or evaluate any machine learning model without separate written consent. Require the processor to identify any sub-processors involved in AI development and to certify that training data pipelines are isolated from production data.
- Build in cross-border transfer flexibility with fallback mechanisms: Do not rely on a single transfer mechanism. Structure the clause so that the primary mechanism is the EU-US Data Privacy Framework (if the processor is certified), with SCCs as a contractual fallback if the framework is invalidated, and data localization as a last resort. This layered approach prevents a single regulatory decision from disrupting data flows overnight.
Common Pitfalls
- Treating the DPA as boilerplate: Many organizations sign the vendor's standard DPA without negotiation, assuming all DPAs are equivalent. They are not. Standard vendor DPAs typically favor the processor: broader processing permissions, longer breach notification windows, limited audit rights, and capped liability. Review every DPA against your organization's risk profile and regulatory obligations before signing.
- Failing to map data flows before drafting: You cannot draft an effective DPA if you do not know what personal data is being processed, where it flows, and which sub-processors handle it. Conduct a data flow mapping exercise before negotiation. Without this, you will miss categories of personal data (e.g., metadata, IP addresses, device identifiers) that may trigger additional regulatory requirements.
- Ignoring the deletion timeline: Most DPAs require the processor to delete or return personal data after the service ends, but few specify a concrete timeline. Without a deadline (e.g., "within 30 days of termination"), data can persist indefinitely in the processor's backups and archives. Specify a deletion deadline, require written certification of deletion, and address backup retention separately.
- Overlooking sub-processor chain liability: Your DPA with the primary processor is only as strong as the processor's agreements with its sub-processors. If a sub-processor causes a breach, your recourse depends on whether the primary processor has flow-down obligations in place. Require the processor to ensure that each sub-processor is bound by data protection obligations no less protective than those in your DPA, and that the processor remains fully liable for sub-processor breaches.
- Relying solely on SOC 2 reports as audit substitutes: SOC 2 Type II reports are useful but limited. They cover the controls the auditor was asked to evaluate, not necessarily the controls that matter for your data. If you accept SOC 2 as an audit substitute, review the report scope to confirm it covers the specific services and data categories relevant to your contract. Reserve the right to conduct targeted audits for material concerns or following a security incident.
Key drafting notes for a Data Protection Clause:
- Get the definitions right: Define "personal data," "processing," "controller," and "processor" in a way that actually matches your relationship. Many contracts mislabel roles - you think your vendor is a processor but they're actually a co-controller if they're using the data for their own purposes too.
- Address AI model training explicitly: If the processor or any sub-processor might train AI models on your data, spell it out or forbid it. Many vendors quietly feed customer data into LLM training. In 2025-26, this is a major negotiating point.
- Schrems II compliance: If transferring data from EU to US, use the Data Privacy Framework (if your vendor is certified) or SCCs plus a supplementary assessment that the country's surveillance laws don't pose a risk to the data. Document this risk assessment.
- Sub-processor list must be kept current: Your vendor will add new sub-processors over time (cloud providers, analytics, etc.). Require them to notify you in advance and give you a 30-day objection period. If you object to a sub-processor, you should have the right to terminate the contract without penalty.
- Breach notification is everything: Require notification within 24 hours of discovery, not discovery. The faster you know, the faster you can notify regulators (72-hour GDPR deadline is real). A delayed notice can mean the difference between a warning and a fine.
Historic note:
GDPR (2018) upended data processing contracts overnight. Before 2018, data protection clauses were afterthoughts in most vendor contracts. GDPR forced organizations to actually define controller-processor relationships, implement SCCs, and take data security seriously. The Schrems II ruling (July 2020) muddied EU-US data transfers, invalidating Privacy Shield and putting SCCs under legal cloud until the EU-US Data Privacy Framework arrived in 2023. The collapse of the Privacy Shield framework showed how fragile transatlantic data deals are - one court ruling can demolish them. California's CCPA (2020) and subsequent state privacy laws created a domestic US complexity that GDPR had already introduced in Europe. Now, with the EU AI Act (2025-26), COPPA 2.0, and India's DPDP Act in force, data protection clauses have exploded in scope and complexity.
Jurisdiction specific notes:
- U.S.: The Federal Trade Commission (FTC) enforces data privacy for most companies under Section 5 of the FTC Act. State laws (CCPA, VCDPA, CPA, CTDPA, UTIPA) have different consent, opt-out, and deletion requirements. Health data is HIPAA (or HITECH for business associates). There is no single federal framework like GDPR, so a US company processing data from multiple states needs compliant terms with each state's requirements. Standard Contractual Clauses are acceptable for US processors under the Data Privacy Framework, but not all US companies are certified.
- U.K.: The UK Data Protection Act 2018 mirrors GDPR but is enforced by the ICO (Information Commissioner's Office). Post-Brexit, the UK is an "adequate" jurisdiction for GDPR purposes, meaning personal data can flow from EU to UK relatively freely. However, UK-US data transfers face similar Schrems II-like issues as EU-US transfers. UK companies processing children's data must meet the Age Appropriate Design Code.
Drafting tip:
For multinational contracts, consider a modular DPA that says: "Base DPA terms apply to all jurisdictions, plus the following jurisdiction-specific addendum for [EU / US / UK / India / etc.]." This keeps the agreement manageable while meeting local law requirements.










.avif)


